-
Check out the Systrace Blog.
Systrace - Interactive Policy Generation for System Calls
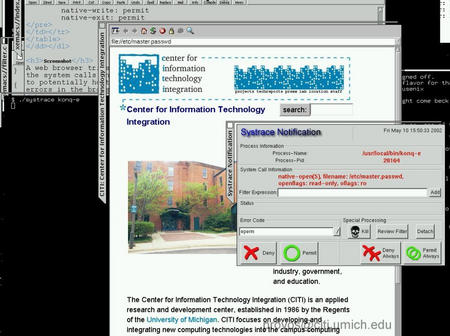
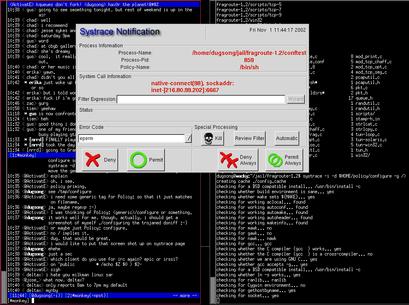
Systrace enforces system call policies for applications by constraining the application's access to the system. The policy is generated interactively. Operations not covered by the policy raise an alarm, allowing an user to refine the currently configured policy. For complicated applications, it is difficult to know the correct policy before running them. Initially, Systrace notifies the user about all system calls that an application tries to execute. The user configures a policy for the specific system call that caused the warning. After a few minutes, a policy is generated that allows the application to run without any warnings. However, events that are not covered still generate a warning. Normally, that is an indication of a security problem. Systrace improves cyber security by providing intrusion prevention.
Alternatively, policies can be learned automatically. In many instances, the automatically learned policies can be used for sandboxing immediately. Sometimes, minimal manual post-processing is necessary.
With Systrace, untrusted binary applications can be sandboxed. Their access to the system can be restricted almost arbitrarily. Sandboxing applications that are available only as binaries is only sensible, as it is not possible to directly analyze what they are designed to do. However, constraining the system calls that large open-source applications are allowed to execute is useful too, as it is very difficult to determine their correctness.
System call arguments can be rewritten dynamically. This effects a virtual chroot for the sandboxed application. It also prevents race conditions in the argument evaluation.
[Answers to some frequently asked questions]
Features
- Confines untrusted binary applications.
- Interactive Policy Generation with Graphical User Interface.
- Supports different emulations:
- GNU/Linux, BSDI, etc..
- System Call Argument Rewriting.
- Non-interactive Policy Enforcement.
- Remote Monitoring and Intrusion Detection.
- Privilege Elevation: Add-on capabilities.
Intrusion Detection
With Systrace, it is possible to monitor daemons on remote machines and generate warnings at a central location. As these warnings indicate operations not covered by existing policy, it is possible to detect intrusions and prevent them from succeeding. For example, a web server or ftp server can be monitored that way.Non-Interactive Policy Enforcement
Once a policy has been generated, Systrace can enforce it automatically without user interaction. System calls not covered by the existing policy are denied. For example, a shell provider can enforce policy of user shells and executed commands with Systrace.Privilege Elevation
Using the privilege elevation feature of Systrace, it is possible to completely remove the need of setuid or setgid binaries.Instead, Systrace executes the application without privileges and only elevates them to the desired level when required. For example,
-
native-socket: sockdom eq "AF_INET" and socktype eq "SOCK_RAW" then permit as root native-bind: sockaddr eq "inet-[0.0.0.0]:22" then permit as root native-fsread: filename eq "/dev/kmem" then permit as :kmem
Systrace elevates the privileges precisely for the operations that require them. As a result, we get as fine-grained capabilities as possible and the privileged code path is reduced extremely. In combination with dynamic predicates, it is possible to allow an unprivileged application to bind to a reserved port exactly once, etc.
Policy Example
The following example illustrates a simple policy for the ls binary. If ls attempts to list files in /etc, Systrace disallows the access and /etc does not seem to exist. Listing the contents of /tmp works normally, but trying to ls /var generates a warning.-
Policy: /bin/ls, Emulation: native native-munmap: permit [...] native-stat: permit native-fsread: filename match "/usr/*" then permit native-fsread: filename eq "/tmp" then permit native-fsread: filename eq "/etc" then deny[enotdir] native-fchdir: permit native-fstat: permit native-fcntl: permit [...] native-close: permit native-write: permit native-exit: permit
Systrace supports multiple applications with multiple policies. Policies can be switched on execve.
Screenshots
Download
Systrace is distributed under a BSD-style license and has been integrated into NetBSD, OpenBSD and OpenDarwin. NetBSD-current contains the most recent Systrace source code. You can use AnonCVS to access it. At the moment, systrace supports native and Linux binaries.Ports
- GNU/Linux port is finished and kernel patch is maintained actively by Marius Eriksen. Can be run without kernel changes using the ptrace backend.
- Mac OS X port is almost complete; currently unmaintained due to lack of hardware.
- FreeBSD port by Rich Murphey; in progress.
Source Code
You need to install the systrace userland. The gtk frontend is required only for graphical policy generation.- systrace-1.6d.tar.gz [gpg sig] [i386 deb] - 2006-04-23
- more system call translations.
- ptrace: fixed issues with zombies sticking around.
- systrace-1.6c.tar.gz [gpg sig] [i386 deb] - 2006-04-08
- Ptrace: some more work for older 2.4 kernels.
- added translations for chflags, mmap and mprotect.
- systrace-1.6b.tar.gz [gpg sig] - 2006-04-06
- Ptrace: make it work on older 2.4 kernels.
- Ptrace: Detect when headers and kernel are out of sync.
- systrace-1.6a.tar.gz [gpg sig] - 2006-03-26
- Ptrace: support for multi-threading.
- Ptrace: small performance improvement.
- Ptrace: avoid crashing kernels due to ptrace kernel bug.
- systrace-1.6.tar.gz [gpg sig] - 2006-03-24
- Ptrace option for Linux to run without kernel changes.
- usr-systrace-2004-01-26 [gpg sig] - Snapshot of systrace userland. (Darwin, Linux, NetBSD, OpenBSD) - 2004-01-26
- Bunch of features including complete policy updates.
- usr-systrace-2003-06-23 - Snapshot of systrace userland. (Darwin, Linux, NetBSD, OpenBSD) - 2003-06-23
- UI detaching and multiplexing.
- Allows for escaping of special characters.
- Support for prompt directive.
- Freeing of old policies, requires kernel patch for OpenBSD.
- gtk-systrace-2003-06-23 [i386 deb] - GTK Systrace front end invoked by systrace. Install it as /usr/X11R6/bin/xsystrace
- systrace templates - Templates for NetBSD/OpenBSD to facilitate policy generation. - 2002-11-22
References
-
- Improving Host Security with System Call Policies
- Niels Provos, 12th USENIX Security Symposium, Washington, DC, August 2003.
Sample Policies
Links
- Absolute OpenBSD - A book about OpenBSD that includes a chapter on Systrace.
- Systrace has been presented at CanSecWest in May 2002.
- Systrace WIP at the USENIX Technical conference in June 2002.
- Systrace Talk at the Libre Software Meeting in July 2002.
- Firefly - The Complete Series - unrelated but the best Sci-Fi show I have seen so far.
Systrace in the Press
- Creating Systrace Policies, O'Reilly ONLamp.com, February 2003.
- Systrace - A tightly locked jail of legitimate system calls, Linux Magazine, February 2003.
- Verrouillez les appels systemes avec systrace, Login, Nr. 101, December, 2002.
- Enges Korsett - Systrace setzt Regeln für erlaubte Systemaufrufe durch, Linux-Magazin, December, 2002.
Acknowledgements
Thanks to Dug Song and Perry Metzger for helpful discussions and suggestions.